
Audio By Carbonatix
Hackers thought to be working for the North Korean regime have successfully cashed out at least $300m (£232m) of their record-breaking $1.5bn crypto heist.
The criminals, known as Lazarus Group, swiped the huge haul of digital tokens in a hack on crypto exchange ByBit two weeks ago.
Since then, it's been a cat-and-mouse game to track and block the hackers from successfully converting the crypto into usable cash.
Experts say the infamous hacking team is working nearly 24 hours a day - potentially funnelling the money into the regime's military development.
"Every minute matters for the hackers who are trying to confuse the money trail and they are extremely sophisticated in what they're doing," says Dr Tom Robinson, co-founder of crypto investigators Elliptic.
Out of all the criminal actors involved in cryptocurrency, North Korea is the best at laundering crypto, Dr Robinson says.
"I imagine they have an entire room of people doing this using automated tools and years of experience. We can also see from their activity that they only take a few hours break each day, possibly working in shifts to get the crypto turned into cash."
Elliptic's analysis tallies with ByBit, which says that 20% of the funds have now "gone dark", meaning it is unlikely to ever be recovered.
The US and allies accuse the North Koreans of carrying out dozens of hacks in recent years to fund the regime's military and nuclear development.
On 21 February, the criminals hacked one of ByBit's suppliers to secretly alter the digital wallet address that 401,000 Ethereum crypto coins were being sent to.
ByBit thought it was transferring the funds to its own digital wallet, but instead sent it all to the hackers.

Ben Zhou, the CEO of ByBit, assured customers that none of their funds had been taken.
The firm has since replenished the stolen coins with loans from investors, but is in Zhou's words "waging war on Lazarus".
ByBit's Lazarus Bounty programme is encouraging members of the public to trace the stolen funds and get them frozen where possible.
All crypto transactions are displayed on a public blockchain, so it's possible to track the money as it's moved around by the Lazarus Group.
If the hackers try to use a mainstream crypto service to attempt to turn the coins into normal money like dollars, the crypto coins can be frozen by the company if they think they are linked to crime.
So far 20 people have shared more than $4m in rewards for successfully identifying $40m of the stolen money and alerting crypto firms to block transfers.
But experts are downbeat about the chances of the rest of the funds being recoverable, given the North Korean expertise in hacking and laundering the money.
"North Korea is a very closed system and closed economy, so they created a successful industry for hacking and laundering and they don't care about the negative impression of cyber crime," Dr Dorit Dor from cyber security company Check Point said.
Another problem is that not all crypto companies are as willing to help as others.
Crypto exchange eXch is being accused by ByBit and others of not stopping the criminals from cashing out.
More than $90m has been successfully funnelled through this exchange.
But over email, the elusive owner of eXch - Johann Roberts - disputed that.
He admits they didn't initially stop the funds, as his company is in a long-running dispute with ByBit, and he says his team wasn't sure the coins were definitely from the hack.
He says he is now co-operating, but argues that mainstream companies that identify crypto customers are abandoning the private and anonymous benefits of crypto currency.
North Korea has never admitted being behind the Lazarus Group, but is thought to be the only country in the world using its hacking powers for financial gain.
Previously, Lazarus Group hackers targeted banks, but in the last five years, they have specialised in attacking cryptocurrency companies.
The industry is less well protected with fewer mechanisms in place to stop them laundering the funds.
Recent hacks linked to North Korea include:
- The 2019 hack on UpBit for $41m
- The $275m theft of crypto from exchange KuCoin (most of the funds were recovered)
- The 2022 Ronin Bridge attack, which saw hackers make off with $600m in crypto
- Approximately $100m in crypto was stolen in an attack on Atomic Wallet in 2023
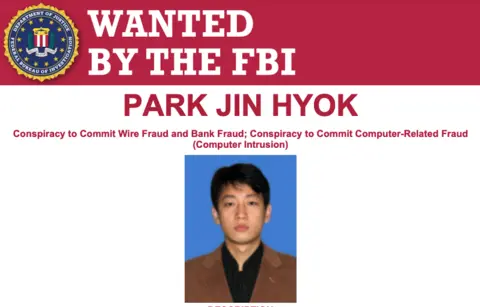
In 2020, the US added North Koreans accused of being part of the Lazarus Group to its Cyber Most Wanted list. However, the chances of individuals ever being arrested are extremely slim unless they leave their country.
Latest Stories
-
Four more men freed from flooded Laos cave after 10 days
3 minutes -
Millions of breast cancer patients could safely avoid chemotherapy, study suggests
5 minutes -
Liverpool sack head coach Slot
6 minutes -
600 more Ghanaians register for evacuation from South Africa – Ablakwa
17 minutes -
First Lady joins mourners at funeral of Sammy Gyamfi’s father-in-law
23 minutes -
Xenophobic attacks: Abu Jinapor warns against retaliatory attacks on South Africans
24 minutes -
Abu Jinapor urges African Union action over xenophobic attacks in South Africa
35 minutes -
Ghanaian teacher was detained at Dulles Airport for over a week after admitting asylum plans
47 minutes -
Novel consultation process on bill caused public confusion – Acting NITA boss
49 minutes -
TVET financing model failing students and employers – Eduwatch boss warns
54 minutes -
Proposed NITA Bill: Effia MP urges stronger stakeholder engagement
56 minutes -
NITA: We’ve been transparent throughout digital bills consultation process – Sam George
1 hour -
CNBC Africa partners KGL Group
2 hours -
NDC amendments have watered down Anti-LGBTQ bill – NPP MP
2 hours -
Technology Consultant warns against expansive regulation in proposed NITA Bill
2 hours

