
Audio By Carbonatix
Cyber criminals who stole thousands of digital files belonging to environmental regulator Sepa have published them on the internet.
The public body had about 1.2GB of data stolen from its digital systems on Christmas Eve.
Sepa rejected a ransom demand for the attack, which has been claimed by the international Conti ransomware group.
Contracts, strategy documents and databases are among the 4,000 files released.
The data has been put on the dark web - a part of the internet associated with criminality and only accessible through specialised software.
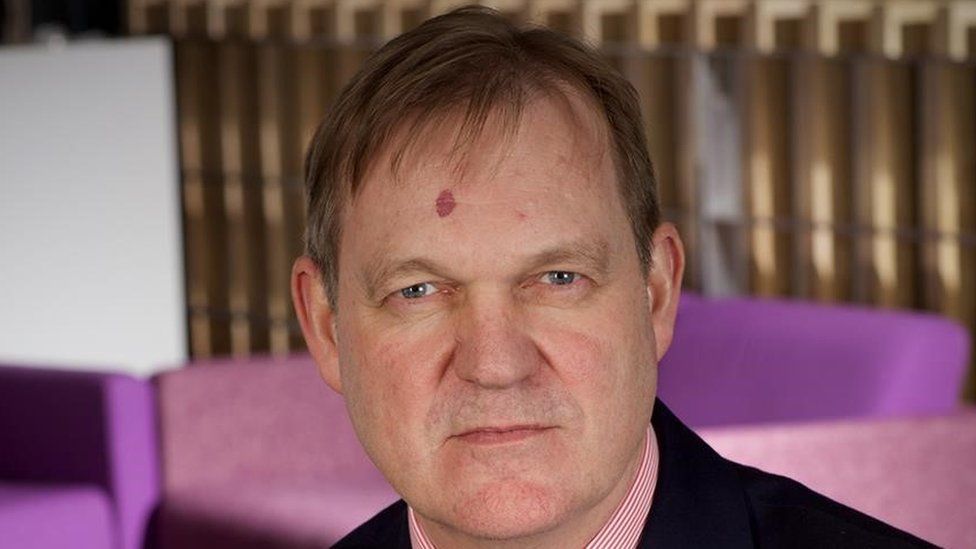
Sepa chief executive Terry A'Hearn said: "We've been clear that we won't use public finance to pay serious and organised criminals intent on disrupting public services and extorting public funds.
"We have made our legal obligations and duty of care on the sensitive handling of data a high priority and, following Police Scotland advice, are confirming that data stolen has been illegally published online.
"We're working quickly with multi-agency partners to recover and analyse data then, as identifications are confirmed, contact and support affected organisations and individuals."
The attack locked Sepa's emails and contacts centre but Sepa said "priority regulatory, monitoring, flood forecasting and warning services were continuing to adapt and operate".
Sepa said the theft was the equivalent to a fraction of the contents of an average laptop hard drive.
Some of the information stolen was already publicly available but other files included data about staff and suppliers was not.
Where information has been identified to date, staff have been contacted and are being supported.
'Serve as a warning to future victims'
Brett Callow, of cyber security company Emsisoft, has been tracking the Sepa ransomware attack.
He said: "Conti may well be the work of the same people behind another type of ransomware called Ryuk.
"There are similarities in the code, ransom note and attack mechanisms.
"When the complete haul of data is posted like this, it usually means the group has given up hope of being able to extract payment from the victim of monetise the data in other ways.
"It's a loss for them. At this point, they've lost all leverage and the action is intended to serve as a warning to future victims."
Det Insp Michael McCullagh, of Police Scotland's cybercrime investigations unit, said: "This remains an ongoing investigation.
"Inquiries remain at an early stage and continue to progress including deployment of specialist cybercrime resources to support this response."

The authorities will be pleased.
It looks like Sepa decided not to play ball with the cyber criminals.
Ransomware is a scourge that is costing organisations billions of pounds and every time a victim pays, it fuels further attacks.
Sadly for Sepa this is far from over.
By the looks of the stash of files that the hackers stole and encrypted, Sepa will have months of work ahead to try to recover important documents and spreadsheets from backups and rebuild their records.
It's also telling that, according to the hackers website, almost 1,000 people have so far looked at the documents.
Who knows what other criminals or hackers are poring over the files right now.
Making the documents open to all means that information can be extracted to potentially be used against Sepa in further attacks or extortion attempts.
It will be months, perhaps even years until the organisation can say it is safe once more and can put this cyber attack behind it.
Latest Stories
-
‘He wanted to take it’ – Gabriel’s first Arsenal penalty ends with heartbreak
55 minutes -
PSG go back-to-back and join ‘greatest of all time’
2 hours -
Ebola spread in DR Congo ‘deeply alarming’, MSF warns
2 hours -
‘It’s like a decaying body’: Australian farmers battle mouse plague
3 hours -
MCL Ghana positions itself at the forefront of Ghana’s emerging luxury real estate economy
3 hours -
Oscar-winning Star Wars editor Marcia Lucas dies aged 80
4 hours -
Italy bans Kanye West and Travis Scott concerts over security concerns
4 hours -
Sight and sound: Fans go into frenzy at Hitz FM Rep Ur Jersey as PSG retain UCL title
4 hours -
Scientists warn dangerous radon gas may be increasing lung cancer risks
5 hours -
EPA, Columbia University partner to map air pollution across Ghana — even in places without monitors
5 hours -
Municipal Assemblies gain real-time pollution data as Breathe Accra expands air quality monitoring network
5 hours -
2026 JoyNews Impact Makers honouree Dr Akunzule donates award prize to support women basket weavers in Upper East
5 hours -
Multimedia Group joins Sammy Gyamfi to mourn late father-in-law
6 hours -
Arsenal heartbreak as PSG win shootout to retain UCL title
6 hours -
Fans go wild at Hitz FM Rep Ur Jersey as PSG retain UCL title in penalty thriller
6 hours

